 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Microsoft is out to prove blockchain naysayers wrong. In an effort to show the potential of the technology beyond its applications in cryptocurrency, the Redmond giant has announced plans to use blockchain tech as the foundation for storing and processing digital identity data.
Following a collaboration with the Decentralized Identity Foundation (DIF), Microsoft has revealed its plans to rely on blockchain technology to solve some of the challenges we face when managing our identities and personal data digitally, such as improving privacy and security across the physical and digital world.
“We believe it is essential for individuals to own and control all elements of their digital identity,” the company said in a blog post. “Rather than grant broad consent to countless apps and services, and have their identity data spread across numerous providers, individuals need a secure, encrypted digital hub where they can store their identity data and easily control access to it.”
To this end, the company is developing an off-chain solution – akin to the Lightning Network – that will allow it to process massive volumes of ID data without congesting the blockchain network. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=Digital+Identity https://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=blockchain

|
Scooped by
Gust MEES
|
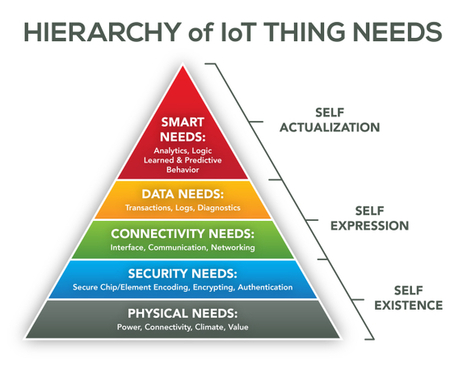
There is no doubt that companies of all shapes and sizes are increasing their spend in internet-of-things (IoT) technology. In fact, IDC projects this to be a $1.4 trillion market by 2021. With the increased spend and demand by consumers for low-price and high-value IoT devices, makers of these connected technologies have put a premium on affordability. The race to the bottom on price has inadvertently created major risks for organizations and consumers, according to PwC’s “Uncovering the Potential of the Internet of Things” report.
The pressure is on, and we see many makers of connected devices that produce IoT products as inexpensively as possible skipping important steps such as the design of security and privacy protections. This is generating significant new risks that are not widely understood during a time when consumers are more concerned about price than privacy and security. Risks include physical, software, encryption and network attacks, all of which could have wide-ranging effects on our daily lives, from taking over a connected car to obtaining sensitive data from a connected home to accessing a private network via a wearable device. Also, there are societal concerns, including getting access to valuable intellectual property, sabotage to companies or governments and espionage. Consumer-focused companies need to ensure they are meeting their customers’ concerns. Simply put, the proper cybersecurity and privacy measures can aid businesses in seeing the full potential of IoT. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=IoT http://www.scoop.it/t/securite-pc-et-internet/?&tag=iot

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
A third of U.S. middle and high school students use mobile devices issued by their schools. Many others use their own devices for their schoolwork, using software such as the widely adopted Google Apps for Education. If you have children in school, chances are good that people and organizations you don’t know are collecting massive quantities of information about your children and using this information for purposes you know nothing about. We don’t know much about how children’s information is used, or by whom, or for what purpose Once data is collected and the company that collected it uses it for its stated purpose, there is little in law or policy that prevents the company from also using the information for other purposes, such as “product development.” It may also sell the information to others for their use or archive it for possible later use. Many bills bearing on student privacyhave been introduced in the past several years in Congress and state legislatures, and several of them have been enacted into law. However, protection of student privacy remains limited. Our recent report explores how corporate entities use their involvement with schools to gather student data and how those data may be used for marketing and other non-school-related purposes. Although most people probably know that digital marketers targetand track children on the devices they use, many would be surprised to learn that schools now serve both as a portal to and reinforcer of digital marketing messages to children. In so doing, they lend companies that collect, sell, analyze, and buy data both enhanced credibility and access to vast amounts of education-related data. Learn more / En savoir plus / Mehr erfahren: https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
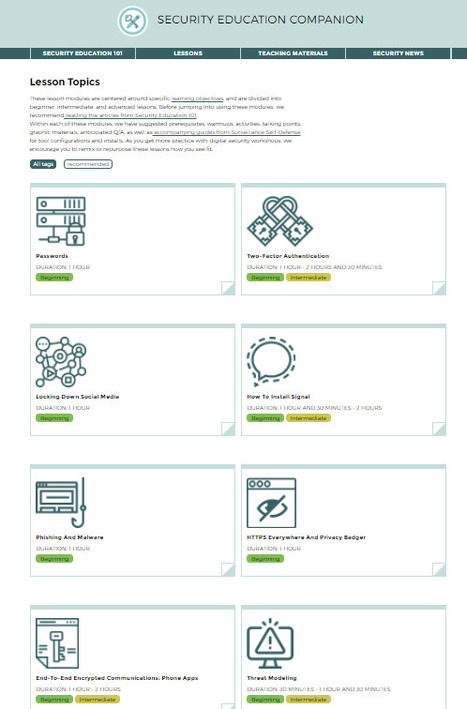
The Security Education Companion is a resource for people teaching digital security to their friends and neighbors. Lesson Topics These lesson modules are centered around specific learning objectives, and are divided into beginner, intermediate, and advanced lessons. Before jumping into using these modules, we recommend reading the articles from Security Education 101.
Within each of these modules, we have suggested prerequisites, warmups, activities, talking points, graphic materials, anticipated Q/A, as well as accompanying guides from Surveillance Self-Defensefor tool configurations and installs. As you get more practice with digital security workshops, we encourage you to remix or repurpose these lessons how you see fit. Learn more / En savoir plus / Mehr erfahren: https://gustmees.wordpress.com/?s=5+minutes

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Yahoo soll für US-Dienste neue Software geschrieben, sie hinter dem Rücken der eigenen Security-Abteilung installiert und damit alle Kundenmails gescannt haben. Juristische Gegenwehr gab es offenbar keine. Ob die Überwachung andauert, ist nicht bekannt. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Yahoo...

|
Scooped by
Gust MEES
|
Niantic Labs, partnering with Nintendo and Pokémon Co., released “Pokémon Go,” a free game for iPhones and Android phones. When you launch it, you see the game franchise’s world famous “pocket monsters” as if they existed in your backyard or bathtub. The point? To “catch ’em all,” as the kids say.
This is augmented reality, or AR, where your smartphone’s camera, GPS and position sensors tell the game what to display and where. It’s a digital world layered over the real one. Unlike virtual reality, which transports you to another universe, you play in your own.
Pikachu is the most well known Pokémon.
The technology isn’t new. Smartphones have had AR games for years, and even Nintendo previously released similar features for its 3DS hand-held device. This isn’t even especially good execution of AR. Which is why perhaps not even Nintendo predicted what happened next. Learn more / En savoir plus / Mehr erfahren: https://gustmees.wordpress.com/2014/11/25/digital-citizenship-social-media-and-privacy/ https://gustmees.wordpress.com/2014/03/05/often-asked-questions-are-there-cyber-security-dangers-with-apps-and-whats-about-privacy/ http://www.scoop.it/t/la-realite-augmentee-augmented-reality-ar

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
We all have something to hide.
The problem with the “nothing to hide” argument is: we’ve all got plenty to hide.
Just today, did you pick your nose? Change clothes? Have sex? Take a shower? Go to the bathroom? Sing off-key in the car on the way to work? Or, maybe you sent an email or text message, a racy photo on Snapchat, or said something inflammatory about your boss.
I bet, if pressed, you’d prefer that most, if not all, of these actions remained private.
And that’s okay.
Privacy is a key part of all our lives. But now that our lives are drifting into the online space, and more with each passing year, why the disconnect between offline and online privacy? The former is desired and expected, while the latter is lauded as wrong and sometimes even criminal.
Separating the desire for privacy from the desire to do something illegal is where it all starts. Too often the two are interwoven into a blanket statement that all those who desire privacy online are doing so out of the necessity to hide nefarious actions.
Learn more / En savoir plus / Mehr erfahren:
https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/

|
Scooped by
Gust MEES
|
|



 Your new post is loading...
Your new post is loading...






























When was the last time you saw a creepy ad on Facebook, which seemed to know about a product you were discussing with a coworker? Or when was the last time you noticed that your Google search had been modified to suit variables like your current location and personal interests?
These micro-events happen on a daily basis for most of us, and are reminders of how valuable and how ubiquitous our data really is. Data is the currency of the new world, and with 2.5 quintillion bytes of data created each day, that status isn’t going away anytime soon.
The problem is, data scientists and analysts are constantly talking about the potential for how to use this data, but too few are talking about the ethics. If we’re going to keep pushing for better systems built on big data, we need to democratize and popularize the ethical conversation surrounding them.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=Ethics
https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/
https://www.scoop.it/t/securite-pc-et-internet/?&tag=tracking
https://www.scoop.it/t/securite-pc-et-internet/?&tag=Privacy
https://www.scoop.it/t/securite-pc-et-internet/?&tag=Big+Data